
Post by : Anees Nasser
The dark web continues to be a hub for illegal trades, but recent observations reveal a significant transformation in the landscape. Cybersecurity experts and threat intelligence groups report that dark web data markets are not just growing; they are becoming more sophisticated. The nature of listings is changing, categories are expanding, and sellers are adjusting to new digital behaviors.
Gone are the days when stolen data was limited to credit card numbers and passwords. A more complex marketplace is emerging that reflects how individuals interact online and protect their personal information. The evolution of these markets points to not just cybercriminal creativity but also emerging risks as businesses and consumers grapple with protecting sensitive data.
This analysis looks at the factors driving these changes, the novel types of data now being traded, the rise of automated sales in underground markets, and what both consumers and organizations need to do to mitigate this growing threat.
Once predictable, dark web listings now showcase an astounding array of data. This evolution is in line with how the digital ecosystem processes and stores personal information.
New categories include:
behavioral data profiles
device fingerprints
cloud-storage tokens
cryptocurrency exchange logins
personal health documents
biometric data
ride-hailing account information
digital wallet recovery phrases
These new categories underscore the shift toward multifaceted digital lifestyles. Cybercriminals have diversified their offerings to exploit interconnected vulnerabilities.
A noticeable trend in the latest listings is the emphasis on “verified” and “fresh” data. Current offerings include:
recently stolen login credentials
verified financial accounts with active balances
up-to-date identity profiles
authenticated device information
tested cloud access tokens
Many sellers now include proof through screenshots or session IDs to assure buyers of the quality of their data.
This reflects a more consumer-like mentality where reliability and utility take precedence, enabling high-quality listings to command premium prices.
A notable trend is the emergence of subscription services within dark web markets. Sellers are providing:
monthly data packages
recurring access to updated credentials
scheduled dumps from compromised devices
weekly cloud storage harvests
subscription access to exclusive data repositories
This shift indicates that these markets are increasingly resembling legitimate business models, as cybercriminals realize the benefits of stable revenue and customer loyalty.
Subscription services are a clear sign that cybercrime is evolving into organized enterprises.
Traditionally, dark web markets have centered on consumer data, but there's a growing trend towards corporate information, including:
internal email communications
system architecture
VPN access credentials
access to cloud dashboards
HR and payroll records
supply chain contracts
These documents are often acquired through:
phishing attacks
hacked employee devices
inadequately secured cloud platforms
Cybercriminals are increasingly attracted to enterprise data due to its high resale value.
There's also a growing demand for behavioral data featuring:
internet browsing habits
app usage trends
location tracking data
purchasing preferences
This information provides cybercriminals with the tools needed to:
execute targeted phishing schemes
bypass security measures
predict user behavior
Unlike traditional data, such as passwords, this type of information doesn't lose its value easily and remains a lucrative target.
With modern applications relying heavily on session tokens, these have become particularly attractive to cybercriminals. Recent listings now include:
stolen cloud sync tokens
authentication cookies
tokenized identity credentials
Tokens enable high-level account access without triggering alerts, illustrating a shift towards stealthier cyberattack methods.
While direct extraction of biometric identifiers is rare, associated data is starting to show up on underground platforms. This encompasses:
facial recognition calibration files
partial biometric metadata
Although not directly usable for device access, they can facilitate identity theft and fraud.
Crypto-related data listings are on the rise, featuring:
seed phrases
exchange account credentials
With the fluctuation of cryptocurrency markets, cybercriminals are quick to target unsuspecting users unaware of security protocols.
The evolution towards automation is changing the dark web landscape. Sellers now utilize:
robots for quick data delivery
automated data scraping
Automation enhances transaction speed and attractiveness, reducing seller risks associated with direct customer interaction.
Trust is essential in dark web markets, and reputation is built through:
customer ratings
reviews and refund policies
This development illustrates the increasingly structured economy where reliability determines income potential.
Numerous parallel services are surfacing, such as:
offerings for cryptocurrency conversions
recruitment channels
This surge indicates a streamlined cybercrime ecosystem, allowing for more effective monetization of stolen information.
Dark web markets are cyclical; as outdated platforms fade, new ones with enhanced security measures and features are appearing. These new venues boast:
better security policies
more efficient interfaces
The quick turnover poses ongoing challenges for law enforcement.
The shifting dark web data market landscape has critical implications for both consumers and businesses.
Varied data types permit more sophisticated targeting.
Greater enterprise data listings heighten corporate spy threats.
Behavioral and token-based data circumvent traditional security measures.
Automation enables a larger pool of active attackers.
Consumers are encouraged to adopt stringent security practices.
Employ distinct passwords across various platforms.
Utilize multi-factor authentication whenever feasible.
Avoid keeping sensitive data in unencrypted folders.
Organizations should fortify their data protection protocols.
The evolution of dark web data markets reflects broader cybersecurity challenges. With automated processes and diverse data types continuously emerging, both individuals and organizations must remain vigilant in their data protection efforts.
This overview sheds light on cybercrime patterns; it does not implicate specific actors. Consult cybersecurity experts for tailored advice.







Anticipated Dates for UAE Eid Al Adha 2026 Unveiled by Astronomical Experts
Experts predict Eid Al Adha 2026 in the UAE to start on May 27, prompting early holiday planning amo

DAE Achieves Remarkable Growth in Q1 2026 With Record Revenue
Dubai Aerospace Enterprise announces impressive financial results for Q1 2026, reflecting a surge in

Price Increase for Sony PS5 in Southeast Asia Effective May 1
Sony announces a price increase for the PS5 across Southeast Asia starting May 1, 2026, impacting ga

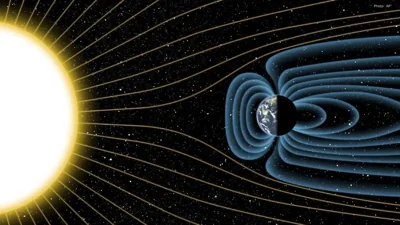
Potential ‘Super El Niño’ in 2026: Understanding the Climate Risks
Could a Super El Niño emerge in 2026? Discover its implications and potential global climate impacts

Global Energy Crisis Intensifies: Markets React to Oil Supply Challenges
Markets are on edge as oil disruptions escalate, influencing prices and economic stability. Explore

Must-See Tourist Spots in London You Can't Overlook
Explore London's essential attractions, from royal landmarks to vibrant markets, ensuring an unforge