
Post by : Anees Nasser
The landscape of cybersecurity has undergone a significant change. What was once speculative has become a pressing reality: AI-driven cyberattacks are now commonplace. Malicious actors utilize AI algorithms and automated systems to conduct rapid network scans, tailor phishing attempts, and exploit weaknesses before response teams can act.
The speed of these recent assaults has fundamentally altered the rules of engagement. Previously, cyberattacks required human oversight, manual scanning, and repeated attempts to breach defenses. With AI, attackers can perform continuous, extensive scans across the internet, evaluating thousands of targets per second. This new capability accurately detects weak passwords, outdated software, unpatched vulnerabilities, and exposed services meticulously.
As this activity is largely automated, attackers no longer struggle with fatigue or time constraints. They can transition from discovery to exploitation within minutes, shrinking the traditional patch window that IT departments relied on. Rather than having days or weeks to address vulnerabilities, organizations are now at risk of attacks within hours of a newly discovered fault.
A recent wave of attacks showcased how AI systems could conduct reconnaissance, create exploit sequences, and maneuver laterally within networks without needing ongoing human involvement. These tactics underscore that the threshold for entry into cybercrime has lowered, while the sophistication of attacks has surged.
Consequently, routine patching and configuration management have escalated to become imperative priorities.
Cybercriminals leverage AI to amplify nearly every phase of a cyber attack. Here are the main threat categories that organizations need to recognize.
Perhaps the most concerning application of AI in cybercrime is automated reconnaissance. AI technologies probe assets including public domains, cloud endpoints, login portals, APIs, IoT devices, and unmanaged servers.
Modern AI scanners can:
identify outdated software
detect open ports
uncover misconfigurations
reveal weak identity controls
find forgotten but exposed assets
This reconnaissance is relentless. An organization that neglects even a single update risks being identified by an AI-powered scanner within hours.
Phishing attacks have significantly increased in sophistication. Attackers employ AI to scrutinize employee profiles, harvest public data, mimic writing styles, and produce tailored messages that appear genuine. These communications cater to the recipient’s role, history, and industry-specific language, thus heightening the chances of interaction.
Additionally, AI can generate deepfake audio, compose realistic scripts for phone scams, and facilitate chat-based exchanges that mislead users into sharing credentials or approving access requests. IT personnel must consider that phishing attempts now blend seamlessly with genuine communications.
A particularly alarming trend is the ability of AI tools to aid attackers in crafting or altering exploits. Rather than resorting to published kits, attackers now utilize AI to:
construct exploit codes
enhance payloads
test variations against security defenses
design new credential exploits
tailor exploits for specific platforms
This advancement eliminates delays that previously existed between vulnerability disclosure and exploit development.
AI assists attackers in identifying lawful system tools which they can weaponize. This “living-off-the-land” strategy allows them to function without deploying traditional malware, complicating detection efforts.
AI supports attackers by:
mapping network layouts
spotting high-value accounts
navigating laterally through unmonitored credentials
silently escalating privileges
camouflaging malicious activities within normal traffic
This stealthy approach poses one of the greatest threats to corporate security.
Below are immediate steps that IT departments must consider as non-negotiable in the face of escalating AI-driven threats.
Addressing this is the foremost priority. AI scanners can identify unpatched devices swiftly, making them significant vulnerabilities.
IT teams should:
ensure all operating systems are up to date
distribute patches across servers and devices
prioritize vulnerabilities deemed 'critical'
actively tackle flaws known to be exploited
validate patch deployment to confirm success
Automated verification is vital, as failed patches can often go unrecognized, becoming prime targets.
Attackers frequently exploit forgotten services that organizations fail to secure.
IT teams should promptly examine:
remote desktop ports
SSH access
VPN gateways
cloud-facing administrative consoles
management interfaces for IoT or OT
outdated legacy servers
Inadequately protected services should be disabled, restricted, or adequately authenticated.
Firmware updates for routers, switches, and IoT devices are equally critical, as such systems often fall behind in their security upgrades.
Multi-factor authentication (MFA) is now essential. The sophistication of AI-driven phishing makes relying solely on passwords inadequate.
Key measures include:
mandating MFA for all privileged accounts
securing cloud accesses with robust authentication
evaluating unused accounts
applying least-privilege access principles
ensuring access levels are appropriate for roles
AI tools can swiftly identify accounts with elevated permissions and outdated protections, making these high-value targets.
Conventional security measures based on signatures are insufficient. AI-driven attacks often manifest as unusual behaviors rather than identifiable malware.
IT teams should:
refresh endpoint detection and response systems
activate behavioral analytics
set up monitoring for atypical activities
review firewall and intrusion detection rules
implement zero-trust segmentation
Tools must be adjusted to spot unusual patterns such as mass scanning, unexpected processes, or atypical credential use.
APIs serve as prime access points for attackers due to frequent misconfigurations.
IT teams need to:
audit API gateways
refresh outdated credentials
eliminate unnecessary permissions
restrict roles with excessive cloud access
ensure auditing logs are functional
Cloud structures require special attention, given their complex permissions and expansive attack surface.
You can’t secure assets you aren't aware of.
Organizations should:
maintain an exhaustive asset inventory
catalog servers, laptops, IoT systems, and cloud resources
apply automated patch management
ensure patching effectiveness through reporting
Reliance on manual processes opens vulnerabilities that AI-assisted attackers can easily exploit.
IT teams must be aware of evolving attack strategies, emerging vulnerabilities, and ongoing threat activities. AI-driven assaults are swift, making consistent vigilance crucial.
Proactive measures should focus on:
tracking threat intelligence feeds
observing abnormal authentication attempts
noticing rapid scanning behaviors
detecting unexpected service activations
Threat intelligence should guide patching initiatives and security measures.
Humans are still key targets. Even with robust technical measures, a single click on an AI-crafted phishing attempt can jeopardize a whole network.
Training should cover:
identifying personalized phishing attempts
recognizing deepfake voice scenarios
safeguarding against suspicious attachments
ignoring unsolicited password-reset prompts
promptly reporting suspicious interactions
Instilling a strong security culture is vital.
AI-driven attacks necessitate rapid responses. Updated incident response protocols should include:
swift isolation procedures
early detection of lateral movements
shutting down emergency access
plan restoration workflows
outline communication steps
Conducting practice exercises will ensure teams react decisively in genuine situations.
Attackers frequently exploit vulnerabilities in the supply chain—especially from vendors with weak security. AI facilitates the identification of these external vulnerabilities.
IT teams should:
examine vendor access
enforce security standards in contracts
restrict third-party permissions
closely monitor external integrations
Building a robust security framework entails fostering dependable partnerships.
AI eliminates the time buffers that defenders once relied upon. Vulnerabilities that previously took weeks to exploit may now be targeted in a matter of hours. Automated scanning systems can assess thousands of IP addresses in seconds, searching for misconfigurations and outdated patches.
This means:
delaying a patch can lead to an attack
neglecting to close an unused port creates an easy entry
granting excessive access privileges opens takeover paths
disregarding cloud misconfigurations allows for quick exploitation
Securing your network is now a race—and AI has accelerated the adversary.
AI-powered cyber threats signify a crucial shift in cybersecurity. Attackers are now quicker, more dedicated, and better equipped than previously. The only effective defense strategy is rigorous execution across patching, configuration management, access control, and user education.
IT teams must embrace a culture of unyielding vigilance. Every patch is crucial. Every configuration is significant. Every employee must be aware. Organizations that act decisively will stay ahead of AI-driven threats, while those that procrastinate will face heavy consequences.
AI has altered the threat environment. It’s now up to defenders to modify their approach to security.
This article offers general cybersecurity advice. Organizations should tailor their security strategies based on specific systems, risk assessments, and professional evaluations.







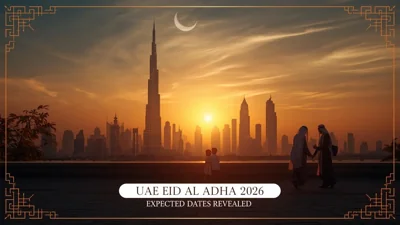
Anticipated Dates for UAE Eid Al Adha 2026 Unveiled by Astronomical Experts
Experts predict Eid Al Adha 2026 in the UAE to start on May 27, prompting early holiday planning amo

DAE Achieves Remarkable Growth in Q1 2026 With Record Revenue
Dubai Aerospace Enterprise announces impressive financial results for Q1 2026, reflecting a surge in

Price Increase for Sony PS5 in Southeast Asia Effective May 1
Sony announces a price increase for the PS5 across Southeast Asia starting May 1, 2026, impacting ga

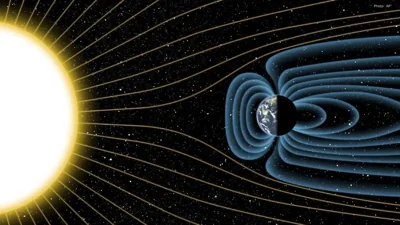
Potential ‘Super El Niño’ in 2026: Understanding the Climate Risks
Could a Super El Niño emerge in 2026? Discover its implications and potential global climate impacts

Global Energy Crisis Intensifies: Markets React to Oil Supply Challenges
Markets are on edge as oil disruptions escalate, influencing prices and economic stability. Explore

Must-See Tourist Spots in London You Can't Overlook
Explore London's essential attractions, from royal landmarks to vibrant markets, ensuring an unforge